Learn Free software with me!
Student projects: PhisSticks BadUSB simulation (video) Cryptocurrency mining dashboard; Analysing software radio with machine learning; student tag; course projects.
Popular docs: Calendar.txt (HN #1), Install Debian on Virtualbox, Command Line Basics Revisited, Micro editor plugins, Kanasirja offline reference, Cracking passwords with Hashcat, Install WebGoat 8 - Learn Web Pentesting, Crack file password with John, Fuzz URLs to find hidden directories, Translate Offline with AI. Tero's books on Amazon, over 500k sold.
Haaga-Helia offers 25 credits of offensive security courses + 15 credit thesis. And that's just for the offensive side...
Courses 2025p1 early autum. Completed. Linux Palvelimet (Linux Servers), Information Security, Tunkeutumistestaus (penetration testing), Sovellusten hakkerointi ja haavoittuvuudet (application hacking / reverse engineering).
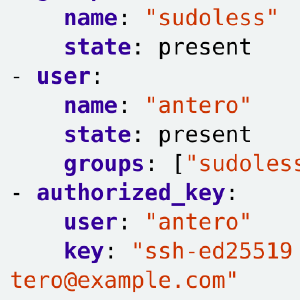
Course 2025p2 late autumn. Ongoing. Palvelinten Hallinta (infra as code, configuration management), Verkkoon tunkeutuminen ja tiedustelu (Network Attacks and Reconnaissance), Cyber Security (Masters).
Courses 2026 early autumn. Enroll in Peppi 2025-11-26 w48 Wed 08:00: Application Hacking and Vulnerabilities (once in English!), Sovellusten hakkerointi ja haavoittuvuudet, Information Security, ICT Infrastructure project (AD hacking, malware keyboard, SDR AI analysis...).