My students Niko Heiskanen and SharkTal wrote a book shop, hlgbooks.com
Buy Niko's booklet "Paypal Integration", 1 EUR. The shop is more beta than the greek letter β, but you can buy from their website if you register first.
And yes, you can have the source code.
Create your own project with your team. Feedback 4.7 excellent.
Previous projects: evil USB keyboard, AI log analysis, physical access control, encrypted communications with free software... What will you build?
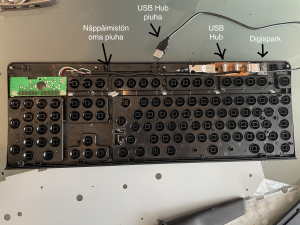
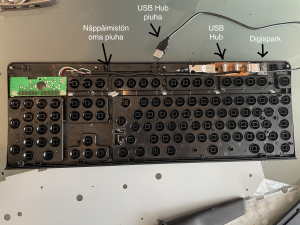
Don't connect that USB stick you found! Hostile USB can take over your computer, install malware and keyloggers.
My students are developing USB attacks and defences. They have built a cheap and customizable hostile USB device
on DigiSpark development board.
Read on to see how to build a hostile USB device similar to "Rubber Ducky" or "BadUSB". And how to defend against this attack.