Trust to Blockchain 2024
ICT Security Basics - from Trust to Blockchain - ICT4HM103- 2024 Late Autumn
Learn security fundamentals to understand current trends. Blockchains, TOR network and video conference encryption all stand on these fundamentals.
Excellent 4.9 out of 5 feedback.
Archived page
This page is archived.
Are you looking for the latest Cyber Security course page? It supersedes this course.
| Course name and code | ICT Security Basics - from Trust to Blockchain - ICT4HM103-3006 Study guide |
| Timing | 2024 period 2 late autumn, w43-w50 |
| Credits | 5 cr (masters level) |
| Classes | Thu 17:40 - 20:30, online, mandatory participation |
| Max students | 30 |
| Language | English |
| Remote | Yes, fully remote |
| Feedback | 4.9 / 5 * Excellent feedback  |
| Services | Moodle: Trust to Blockchain, Jitsi, Laksu. Voluntary extra: Tero's list. |
| First class | 2024-10-24 w43 Thu 17:40, Jitsi video conference link is in Moodle |
* Best feedback average for course was 4.9/5 excellent, lowest was 3.9/5 "very good".
Learning goals
In this course, you will
- Learn fundamentals of computer security
- See them in hands on exercises
In detail, you'll
- Have an idea of computer security fundamentals (confidentiality, ...)
- Can put infosec tools in perspective, and have tested some of these tools
- Adversarial view - Can take attacker view (at least on a hypothetical level)
- Can relate information security to real life impacts
- Has had a look on some concurrent security tools and techniques
This course gives you grand overview of security principles and practice with tools implementing these principles. Even though you're expected to be able to install and configure programs and troubleshoot some errors, this is not my most technical course. If you want a demanding, hands on ethical hacking course, pick Tunkeutumistaus (Penetration Testing), Sovellusten hakkerointi ja haavoittuvuudet (Application hacking) or Verkkoon tunkeutuminen ja tiedustelu (Network Attacks and Reconnaissance) in addition to this.
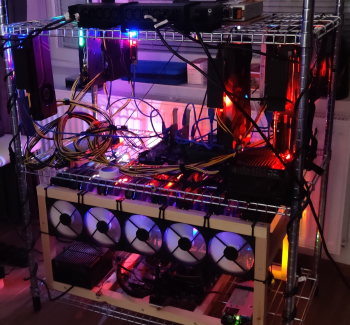
Photo shows Mika Hirvelä's cryptomining rig, photo by Hirvelä.
Agenda
I will keep updating the subjects, but you can write dates to your calendar right away.
Every class is on Thursday evening, 17:40 - 20:30. It's video conference trough Jitsi, mandatory participation.
You can keep your presentation any suitable day, even on week two. Earlier is better. Email Tero to reserve a slot.
| Date | Subject |
|---|---|
| 2024-10-24 w43 Thu | 1. Welcome words. Overview of the course. |
| 2024-10-31 w44 Thu | 2. Fundamentals. Threat model. Lauri: Blockchain, cryptocurrencies and their practical applications (L). Heidi: Securing IT with non-IT people. |
| 2024-11-07 w45 Thu | 3. Satu: STRIDE. Juuso: Why Cloud is safer than on-prem. Kati: Infosec for B2B Logistics Company. |
| 2024-11-14 w46 Thu | 4. Tomi: OWASP 10. Juha-Matti: Customer service security protocols. Jori: Physical security - my observations on public sector. Bitcoin intro. |
| 2024-11-21 w47 Thu | 5. Helsec event (physically or through stream) |
| 2024-11-28 w48 Thu | 6. Tatu: Don't trust that storage medium. Jarna: GDPR. Perttu: Gamification of security awareness training. Bitcoin. |
| 2024-12-05 w49 Thu | 7. Mirella: Log management. Antti: Passwords. Sami: Smart device spying solutions. Lornah: Navigating ICT Security in modern office management. |
| 2024-12-12 w50 Thu | 8. Recap. Martin: Security awareness campaigns. Deepak: Securing Cloud Infrastructure. Hanna: DORA, EU Digital Operational Rescillience Act. Last presentations. |
(L) Longer timeslot.
Last time we had a couple of presentations every class, starting from second week. It worked great, I hope you reserve your slots early. You can present in any class, the earlier the better.
Evaluation
Homeworks 60% and presentations 40%. Evaluation is based on totality of the skills and knowledge demonstrated.
Online classes require active participation. No tapes are provided.
Literature and links
(Haaga-Helia users should have free access to O'Reilly Learning aka Safari Online trough our library, even when they are marked with € below)
r1 Overview, concepts and fundamentals
- OWASP 10 pdf, p 21-22: Note About Risks; Details About Risk Factors.
- Schneier 1999: Modeling security threats (Attack trees)
- Darknet Diaries . (You can find interesting security incidents here. It's hours and hours of material, so just have a look. To listen to podcasts on Android, you can use AntennaPod from F-Droid)
- Krebs on Security (It's a whole blog, so just have a look. You can find security incident writeups here)
- MITRE ATT&CK (Tactics, techniques and procedures. It's big, it's enough to just have a look. )
- Hutchins et al 2011: Intelligence-Driven Computer Network Defense Informed by Analysis of Adversary Campaigns and Intrusion Kill Chains (cyber kill chain)
r2 Blockchain to Cryptocurrency
Nakamoto, Satoshi 2008: Bitcoin: A Peer-to-Peer Electronic Cash System. (A colored HTML version. This is the paper that defined and introduced BitCoin. You can skip "11. Calculations" if you don't like sigma symbols. URL and email address on top of the paper seem unbeliveable and added by third party.
Felten et al 2015: Bitcoin and Cryptocurrency Technologies, videos Week 1 (about 1 hour). Requires free registration. If you find it easy to follow, you can also optionally look at week 2 (1,5 h).
r3 Offensive Views
- Karvinen 2020: Remote Learning Tools for Tero's Courses: Install Virtual Xubuntu Linux
- Karvinen 2019: Install WebGoat PenTest Learning Tool on Ubuntu – with Docker (Make sure your address starts with "localhost" when you practice.
- Disobey 2020 Videos were just published. There are hours of videos, just have a look. Antti Virtanen: "I'm in your office" is an easy start.
- MitmProxy on Kali and Xubuntu – attack and testing
r4 CIA Triad and Encryption
- Schneier 2015: Applied Cryptography Chapter 1: Foundations €
- Curtin 1998: Snake Oil Warning Signs: Encryption Software to Avoid
r5 Applications: Pseudonymity
- Shavers & Bair 2016: Hiding Behind the Keyboard: The Tor Browser €
r6 BitCoin and Crypto Currencies
- Määttä et al 2020: Virtuaalivaluuttojen verotus VH/5083/00.01.00/2019. Previous version is available in English. Latest English version was not available in at the time of writing. This is a long document, only read the parts relevant to you.
Give Feedback, please
Thanks already! It's important for me to get feedback from every single participant.
I will read it all (twice+) and make improvements. Please give your feedback to two channels: comment & mynet.
1) Free form feedback as a comment on this page
You can write whatever you want. No need to repeat the questions, but they are here to get you started.
- Did you learn something? Do you now know something you did not know before the course? (Models, frameworks, ideas, tools?)
- Did you do something for the first time? (Used some technique or a tool for the first time?)
- Is this useful? Are these skills and this knowledge useful in companies or your work?
- How did you like the presentations? Interesting subject? Did you like presenting? Commenting presentations?
- Did you find homework useful? Interesting? Challenging enough?
- Feelings: did you enjoy the course? Did you like the atmosphere in the classes?
- How could I improve the course? (I can make almost any change here, if it's important)
- Would you recommend the course? Have you already recommended it? Who would benefit from the course (a colleague, a fellow student)?
2) Numeric feedback to Haaga-Helia feedback system (MyNet / Peppi)
1-worst, 5-best
- Your active participation in studies
- Achieving the learning goals
- The study methods supported learning
- The study environment supported learning
- Benefits to your career
Open, you can copy the same answer you gave earlier
- What promoted your learning?
- How would you develop the implementation / group of implementations further so that the learning goals could be achieved better?
Your overall assessment of the implementation, 1-worst, 5-best
How likely would you recommend the course to your fellow students? 1-worst, 10-best.
Thank you for your feedback, and thank you for our course!
Optional: Keep up with Linux & security, join Tero's list. (And get invitations to visitors on security)
See you in my future courses!
Homework
Homework is due 24 hours before next class starts. Return a link to Laksu and evaluate two.
Link to Laksu is in Moodle.
Homeworks are done with a computer and reported at the same time. If some task does not require performing tests with a computer, it's specied writing in the subtask.
Each homework is returned
- 24 h before start of next lecture
- you can publish your homework report in any website you like
- return a link to Laksu
- cross-evaluate two other homeworks
To save everyone's time, I will remove those from the course who don't return homework.
Github is a convenient place to publish your reports, others are Gitlab and Wordpress.com. I highly recommend publishing your work. But if you don't dare or want to publish, you can put your web page behind a password (e.g. in Wordpress.com, same password for all reports), and share this password with your group. Or use a pseudonym or an alias.
All sources must be refered to: this task page, classes, reports from your classmates, classmate presentations, man pages, the article you found...
Returned link must open the report directly. For example, return link to your "h1-helsec.md", not the front page of your website. Web page must directly open in web browser, so it must be HTML. (Github will automatically convert your Markdown to HTML). Other formats are not accepted (no docx, no pdf, no odx, no xlsx...).
AI and large language models (LLM): You can ask AI or LLM a question and use the answer as facts for your own answer, written in your own words. AI must be marked as a reference, with details such as prompt (and for advanced users system prompts, temperature, jailbreaks...). LLMs tend to hallucinate, so you should check answers from more reliable sources. It's not allowed to generate text with AI or similar technologies. For example, it's not allowed to generate essay answers or summaries with AI, LLM or similar technologies.
The homeworks are official after they are given in the class. Don't start them before, because they might change. I will of course give homeworks based on what we actually talked about.
h0 Hello
This exercise is the first, easy step towards version control systems. Even though you're just clicking buttons on the website, it uses world leading tool git in the background. Git even uses a tree of hashes of blocks, just like Bitcoin.
- a) Create a web page using Github. Return it to Laksu, and cross evaluate two.
Tips
- Read this first: Karvinen 2023: Create a Web Page Using Github
- Write the page in Markdown. Add headings and paragraphs.
- Browse to the page where you can see your new page normally (headings in bigger text than paragraphs). The correct link to return is shown in your browsers address bar.
- Remember to use md suffix, so that the website knows it's Markdown. E.g. "tero.md".
- Normally, the cross evaluation has free form feedback: good, bad, ideas for improvement, tips... But for this h0, there is not much to comment and one sentence is enough. If you can see a page with paragraph and heading, it's a five. (For the rest of the course, in feedback for actual homework (h1, h2...), your classmates will surely appreciate longer and insightful feedback).
h1 Adversarial mindset
You will read the famous cyber kill chain paper. And start your very own hacking lab by installing Linux virtual machine.
You can only start this homework after accepting course rules in Moodle.
x) Read and summarize. Some bullets is enough for a summary.
- Hutchins et al 2011: Intelligence-Driven Computer Network Defense Informed by Analysis of Adversary Campaigns and Intrusion Kill Chains
- Darknet Diaries. Pick one episode. (RSS feed)
- MITRE ATT&CK FAQ explains the ATT&CK Enterprise Matrix. Explain "tactic", "technique" and "procedure" in context of ATT&CK, and give an example of each. The enterprise matrix is big, you can just glimpse/browse it to see what's available instead of reading hundreds of pages.
a) How would you compare Cyber Kill Chain and ATT&CK Enterprise matrix? Who do you think could benefit from these models?
b) Pick a security incident and learn about it. Write briefly about it. Point out the concepts of threat actor, exploit, vulnerability and (business) impact. (You can find writeups about security incidents from Darknet Diaries and Krebs)
c) Install Debian on Virtualbox. Report your work, including the environment (including host OS, the real physical computer used), the steps you took and their results.
d) Voluntary bonus: Use either (Hutchins et al 2011) cyber kill chain or MITRE ATT&CK framework for analyzing a security incident. You can pick any incident you want (even the one you used earlier in this homework), but try to pick a source that gives you enough technical and business detail to do some analysis. (If you're in a hurry, cyber kill chain is much simpler. If you're technically skillful, you might find ATT&CK interesting)
e) Voluntary bonus: What do you consider the fundamentals of security? What are the theoretical foundations you would teach on the first day?
f) Voluntary bonus: Do you think anything is missing from these models, Cyber Kill Chain or MITRE ATT&CK?
Tips:
- Some bullets for each article is enough. You don't need to have all content of the long articles in your summary.
- For the summary, add your own question, idea or comment
- Hutchins et. al. is the cyber kill chain paper.
- Darknet diaries: you'll probably have a different episode from everyone else, as long as you don't take the latest episode.
- To listen to podcasts on Android, you can use AntennaPod from F-Droid or Google Play
- Refer to each source you've used: the course, the task given, the papers, the podcasts - all sources you've used. All sources must be mentioned in every document, page or blog using them. It's enough to just name and link them, you don't need to write another list in the end. In fact, it's imporant to know wich information comes from which source.
- My article Install Debian on Virtualbox explains it pretty well.
- Got stuck with VirtualBox or Linux? Don't worry, computers are like that. Write a detailed report (in your homework) with screenshots. Explain what approaches you took and what happened. List where you found advice or articles. Explain your ideas why it would not work. You'll get help and advise in the class (and that's not all - you'll also get Linux on your virtual machine).
h2 Pubkey
You're using public key encryption every day. If you know what you're doing, it can help you even more.
- x) Read and summarize (with some bullet points)
- € Schneier 2015: Applied Cryptography: Chapter 2 - Protocol Building Blocks, sections
- 2.5 Communications Using Public-Key Cryptography
- 2.6 Digital Signatures
- 2.7 Digital Signatures With Encryption
- 2.8 Random And Pseudo-Random-Sequence Generation
- € Rosenbaum 2019: Grokking Bitcoin:
- Chapter 2. Cryptographic hash functions and digital signatures:
- Digital signatures (8 sections, from "Typical use of digital signatures" to "Private key security")
- Chapter 2. Cryptographic hash functions and digital signatures:
- Karvinen 2023: PGP - Send Encrypted and Signed Message - gpg
- € Schneier 2015: Applied Cryptography: Chapter 2 - Protocol Building Blocks, sections
- a) Pubkey today. Explain how you have used public key cryptography today or yesterday, outside of this homework. In addition to naming the system, identify how different parties use keys in different steps of the system. (Answering this question likely requries finding sources on your own. This subtask does not require tests with a computer.)
- b) Messaging. Send an encrypted and signed message using PGP, then verify and decrypt it. (You can use folders to simulate users, or use two computers or two different OS users. Don't use Tero as a name of any party, unless that's your given name.)
- c) Other tool. Encrypt a message using a tool other than PGP. Explain how different parties use different keys at different stages of operation. Evaluate the security of the tool you've chosen.
- d) Eve and Mallory. In many crypto stories, Eve is a passive eavesdropper, listening on the wire. Mallory malliciously modifies the messages. Explain how PGP protects against Mallory and Eve. Be specific what features, which use of keys and which flags in the command are related to this protection. (This subtasks does not require tests with a computer)
- f) Password management. Demonstrate use of a password manager. What kind of attacks take advantage of people not using password managers? (You can use any password manager, some examples include pass and KeePassXC.)
- g) Refer to sources. Verify each homework report (this and the earlier ones) refers to sources. Every homework report should refer to this task page. It should also have references to any other source used, such as web pages, LLMs, man pages, other reports... References are mandatory, and must be present in every report. (This subtask does not need a report, you can just do it and write "Done." as the answer for this subtask.)
- h) Voluntary, challenging, requires coding: Cryptopals: Challenge Set 1:
- 1 Convert hex to base64 (feel free to use a library for base64)
- 2 Fixed XOR
- 3 Single-byte XOR cipher
- 4 Detect single-character XOR (This looks tough before you have solved 1-3)
h3 Hash
Welcome to the world of hashes!
You'll use hashes for fingerprinting files, protecting passwords and as Bitcoin puzzles. You'll also take the role of the attacker, and crack some hashes with a well known tool, Hashcat.
- x) Read and summarize (with some bullet points)
- € Schneier 2015: Applied Cryptography: Chapter 2 - Protocol Building Blocks: subchapters "2.3 One-way Fuctions" and "2.4 One-Way Hash Functions".
- Karvinen 2022: Cracking Passwords with Hashcat
- Voluntary bonus article (but recommended if you're not familiar with Linux command line): Karvinen 2020: Command Line Basics Revisited
- Voluntary bonus article: € Santos et al 2017: Security Penetration Testing - The Art of Hacking Series LiveLessons: Lesson 6: Hacking User Credentials (8 videos, about 30 min)
- a) Billion dollar busywork. Command 'echo -n "hello"|sha256sum' prints a hash. Try adding something to the string, e.g. 'echo -n 'hello asdf'|sha256sum'. What do you have to add to get a hash that starts with a zero? (Voluntary bonus: How is this related to Bitcoin? Voluntary difficult bonus: How many zeros can you get to the beginning? Voluntary difficult bonus: How does the difficulty raise?)
- b) Compare hash. Create a small text file. Take it's hash (e.g. 'sha256sum tero.txt'). Change one letter. Take the hash again. Compare hashes. What do you notice?
- c) Hashcat. Install hashcat and test that it works.
- d) Dictionary attack. Crack this hash: 21232f297a57a5a743894a0e4a801fc3
- e) How can you make a password that's protected against a dictionary attack?
- f) Voluntary: Two minute job. Try cracking this hash and comment on your hash rate $2y$18$axMtQ4N8j/NQVItQJed9uORfsUK667RAWfycwFMtDBD6zAo1Se2eu . This subtask d does not require actually cracking the hash, just trying it and commenting on the hash rate.
- g) Voluntary bonus: Where do you want to go today? Crack this Windows NTLM hash: f2477a144dff4f216ab81f2ac3e3207d
- h) Voluntary bonus: Embarassingly parallel. Make hashcat work with your display adapter (GPU). Compare hash rate with and without GPU enabled.
- i) Voluntary bonus: My hash. create some hashes of your own, then crack them with hashcat.
- j) John. Install Jumbo John (John the Ripper, open source Jumbo version). Compile it from source code as needed. See Karvinen 2023 Crack File Password With John.
- k) Crack file password with John.
- l) Voluntary bonus: Custom dictionary. What's Elmeri's password?
Loot from Elmeri's machine
$ sudo grep elmik9 /etc/passwd /etc/shadow
/etc/passwd:elmik9:x:1003:1003:Elmeri "9" Elmik,,,:/home/elmik9:/bin/bash
/etc/shadow:elmik9:$1$xpRkwrhq$aXdu7HQirUmuTZW2m8OXs.:18401:0:99999:7:::
Tips:
- You can likely get the paywalled books and videos for free with your Haaga-Helia account, trough Haaga-Helia library's A-Z Databases. This page has a lot of free goodies included in your Haaga-Helia student status. The login page for O'Reilly Learning has our login under the link "Institution not listed?".
- Scheier's book is famous. It's pretty dense, if this was made by a Youtube influencer, you'd get three seasons of videos from the first couple of paragraphs.
- 'sudo apt-get update', 'sudo apt-get install hashcat hashid micro bash-completion'
- In many tutorials, the hackers guess the type of the hash by comparing it to examples. I prefer using 'hashid -m feedd0c5', the right hash type is usually in top three, and the mode number (-m) is the same as the required -m parameter for hashcat.
- You can use rockyou.txt or similar dictionary.
- Some of the practical exercises can be challenging if you're new to the world of hacking. Don't worry, computers are like that. Write a detailed report (in your homework) with screenshots. Explain what approaches you took and what happened. List where you found advice or articles. Explain your ideas why it would not work. You'll get help and advise in the class. As these are the tools that actual hackers and pentesters use, they are more optimized to get the results than being the most beginner friendly.
- Only test on practice data and practice targets. Follow the laws, never point any of these tools to production data or production systems.
- If you're in another juristiction (not Finland), also check the local rules and laws before any pentest related practice.
- If you have not presented yet, you can email Tero to reserve your presentation topic.
- Something to think about: we just learned that hashing is a one-way function. If this is true, why can you crack the hash and find out the original password?
h4 To the moon!
- x) Read and summarize (with some bullet points)
- Nakamoto 2008: Bitcoin: A Peer-to-Peer Electronic Cash System (A colored HTML version), chapters
- 1 Introduction
- 2 Transactions
- 3 Timestamp Server
- 4 Proof-of-Work
- 5 Network
- 6 Incentive
- Nakamoto 2008: Bitcoin: A Peer-to-Peer Electronic Cash System (A colored HTML version), chapters
- a) Wallet. Create a BitCoin testnet wallet. (For example, electrum)
- b) Faucet. Get worthless fake money from a testnet Bitcoin faucet.
- c) Giveway. Move money to another Bitcoin wallet. Choose an amount where the last two digists are 73.
- d) Recycle. Move the testnet money back to the same faucet you got it from.
- e) Explorer. Use a block explorer to analyze a block on the real Bitcoin blockchain. Explain what each value and field means. You only need to analyze the block information and one sample transaction, as a block can contain many transactions. Voluntary bonus: Use a transaction that's interesting, such as one related to a crime or other unusual event.
- f) RogeCoin. Critically comment on Honest Ads: If Cryptocurrency Was Honest (Video, about 5 minutes). Identify and list arguments made. Provide commentary to support and challenge each of the claims. If you can, provide references or real life examples to your claims. (This task does not require tests with a computer.)
- g) Voluntary: Bib39ers. Write a bib39 phrase of a worthless wallet on a piece of paper. Hide it in your house to annoy thieves and others digging your stuff. Or leave it on a background of a photo and post it to social media. Optionally add or change a non-default word as an icing on a cake.
Tips:
- You can use any testnet faucet you want
- Many of them don't seem to work.
- At the time of writing, one working testnet faucet was https://coinfaucet.eu/en/btc-testnet/
- In real life, you must not write your wallet password to a plain text file or a piece of paper.
- With worthless testnet money and these exercises, feel write to write it down. E.g. in your password manager.
- sudo apt-get update; sudo apt-get install electrum; electrum --testnet # from memory
- search
- bitcoin testnet faucet
- bitcoin explorer
- To simulate a fresh install of electrum, 'mv -nv ~/.electrum/ ~/DIS-electrum' (command is from my memory). If you have real wallets (with real money) in electrum, make sure you don't lose the last copy.
h5 HelSec
- x) Watch and summarize. Add your own comments, ideas and questions.
- Two full length HelSec presentations on the November event (2024-11-21 w47 Thu)
- Voluntary bonus: A third one.
- Twitch stream for HelSec
Tips
- Agenda for HelSec November meetup 2024-11-21 w47 Thu
- 18:00 - [Starting words]
- 18:15 - Jos Helmich - Industrial Cyber Security
- 19:20 - Heikki ”zokol” Juva - State of Union
- 20:20 - Joona "Rinorragi" Immonen - My experiences on Defender External Attack Surface Management
- 21:00 - [Flash talks?]
- If you got a ticket, you can watch it in the physical event
- Everyone has a free place in the Twitch stream for HelSec
- We want to watch it live, and it's likely to work. In the unlikely event it does not work (e.g. stream down for more than 30 min), as a backup: you can watch, summarize and comment two full length Helsec or Disobey presentations from their youtube channel. This backup solution is only used if live is unavailable. But most likely everything works and you can watch the live stream.
- HelSec members can get event tickets first. I'm a member and can recommend joining HelSec. Obviously, this is voluntary. And it's not even required to join the event.
h6 Upside Down Iceberg
In Finland, it's legal to use TOR at the time of writing. If you reside in another juristiction, laws might be different. Obviously, it's illegal to do illegal things in TOR, just like it's illegal to do illegal things anywhere. Only do legal things.
If you reside in a jurisdiction where using TOR is illegal, you obviously can't install it and do the related tasks. If you cannot or do not want to do the hands-on darknet tasks, the alternative task is: based on literature only (no hands on tests, no installation), compare anonymous/pseudonymous networks, such as TOR, I2P, Freenet and others. How do their goals, technology and other features differ? How are they similar? Add references. Link differences and benefits to technical and architecture aspects.
- x) Read and summarize (briefly, e.g. with some bullets)
- Dingledine, Mathewson and Syverson 2004: Tor: The second-generation onion router. In USENIX security symposium (jufo level 2). Chapter:
- 3 Design goals and assumptions
- Karunanayake, Ahmed, Malaney, Islam and Jha 2021: De-anonymisation attacks on tor: A survey. In IEEE Communications Surveys & Tutorials (jufo level 2). Chapters:
- Abstract
- I Introduction
- II Background (to the end of "B. Circuit Establishent for Tor HS")
- Fig. 6. Taxonomy for Tor attacks (Just the figure on page 2330.)
- Halonen, Ollikainen, Rajala 2023: PhishSticks - The Ethical Hackers tool for BadUSB (Video, about 3 minutes)
- Dingledine, Mathewson and Syverson 2004: Tor: The second-generation onion router. In USENIX security symposium (jufo level 2). Chapter:
- a) Install TOR browser and access TOR network (.onion addresses). (Explain in detail how you installed it, and how you got access to TOR).
- b) Browse TOR network.
- Find, take screenshots and comment
- search engine for onion sites
- human rights or civil rights organization
- marketplace
- fraud
- forum
- a well known organization (with regular postal addresses, offices or similar presence outside darknet)
- Use .onion addresses inside TOR network, not regular (clearnet) websites trough exit nodes.
- Find, take screenshots and comment
- c) Onion. In your own words, how does anonymity work in TOR? (e.g. how does it use: public keys, encryption, what algorithms? This subtask does not require tests with a computer.)
- d) What kind of the threat models could TOR fit? (This subtask does not require tests with a computer.)
- e) Don't stick that stick. How does PhishSticks attack work? Would a typical organization be vulnerable? Does this link to a broader category of attacks and defenses? How could the risk be mitigated? (This subtask does not require tests with a computer.) (If you want, you can view PhishSticks on Github and PhishSticks Youtube channel.
- f) Voluntary: I2P. Install and demonstrate use of I2P.
- g) Voluntary: Hyphanet. Install and demonstrate use of Hyphanet.
- h) Voluntary: Freenet. Install and demonstrate use of Freenet.
- i) Voluntary: GNUnet. Install and demonstrate use of GNUnet.
- j) Voluntary, difficult: Test PhisSticks USB HID attack on your own computer.
Tips:
- TOR Browser
- Either download it from Tor project homepage, uncompress and launch as we did in the class.
- Alternatively, you could try (from memory) 'sudo apt-get update; sudo apt-get -y install tor torbrowser-launcher; torbrowser-launcher'
h7 Free science!
Follow the new science in infosec.
Jump right into high-quality articles. Save your time, read review article first.
- x) Read and summarize (briefly, e.g. with some bullets)
- Infosec review article.
- Review: Find review article on an infosec area you're interested in
- Peer reviewed: Pick an article on published on a journal that has JUFO rating 1, 2 or 3.
- Fresh: Prefer fresh articles, less than 2 years old.
- Infosec review article.
- a) Voluntary: Create an alert that sends you new peer reviewed articles on your area of intrest. Once it's working, remember to make the filter tighter, so that you're happy when you recieve a message.
Tips
- If the article is long (more than 4 pages), you can skim it for this task and base your summary on skimming.
- Summarize contents, not meta. If you have to do this, note in writing that this is based on skimming.
- Wrong: The article talks about the dangers of cyber criminals in Fobaristan. They go into great details of crimes. There is even a surprising fact!
- Right: Cyber crime has doubled between 2010-2020 in Fobaristan. Main motivator for attackers are criminal profits, driven by unemployment.
- If you want to do voluntary h8, the deadline is the same as with h7.
h8 Bonus
Voluntary bonus. List and link
a) Improved. Any tasks that you have considerably improved after cross review b) Voluntary. Any voluntary bonus tasks you have completed.
If you want to do voluntary h8, the deadline is the same as with h7.